Hack Prevention
Getting Around Nginx IP Restrictions: Disabling Temporary URLs in cPanel
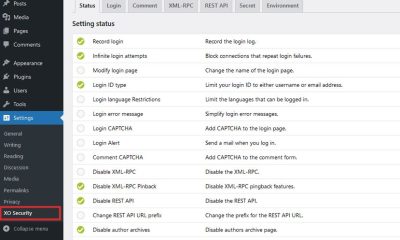
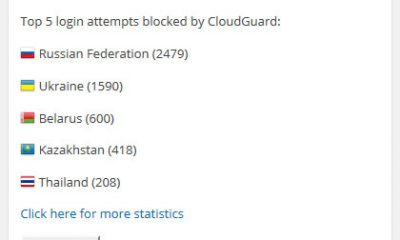
In the past few months, we have covering many ways you can go about protecting your website against hack attacks. You should protect your login page and other parts of your website to make sure hackers don’t breach your walls. I have already covered how you can use plugins such as Limit Login Attempts to stop people from messing with your login and admin pages. Restricting access to your login page by IP is a great idea too. But it is not perfect.
I am using both of the above options plus a few other security layers to keep our sites safe. We are not always successful but try hard. Enabling IP restrictions for your login and admin pages is a great idea but can be rendered useless if someone knows your temporary URLs. That’s why Apache mod_userdir matters:
Apache’s mod_userdir allows users to view their sites by entering a tilde(~) and their username as the uri on a specific host. For example http://test.cpanel.net/~fred/ will bring up the user fred’s domain. The disadvantage of this feature is that any bandwidth usage used by this site will be put on the domain it is accessed under (in this case test.cpanel.net). mod_userdir protection prevents this from happening. You may however want to disable it on specific virtual hosts (generally shared ssl hosts.)
Those of you who rely on cPanel to manage your server have probably seen the above information. Unless you enable mod_userdir protection, hackers will be able to access your login page using temporary URLs. NGINX / Apache won’t be able to stop them (NGINX does not in our case).
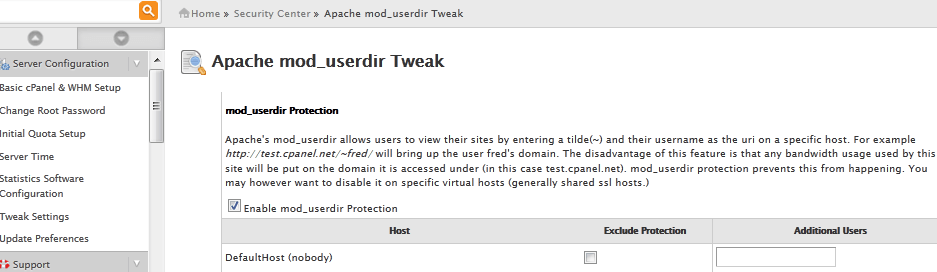
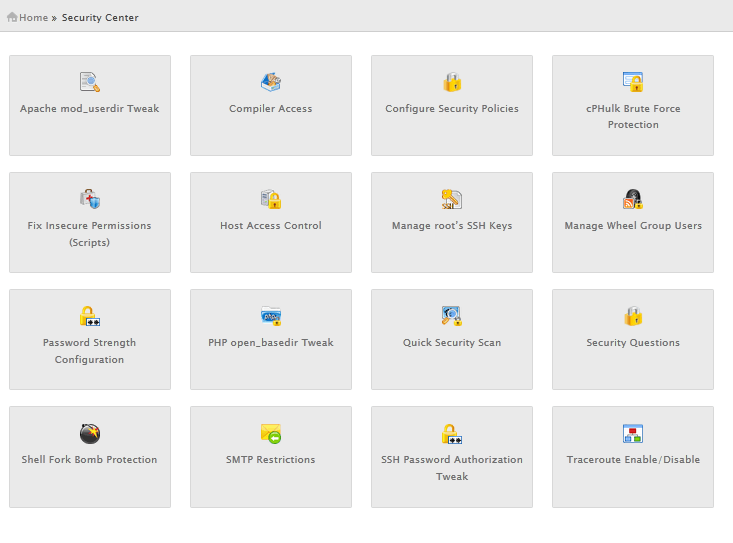
To fix this issue, you should log on to your cPanel account, click on Security Center link, and go to Apache mod_userdir Tweak to enable mod_userdir protection for your website. Keep in mind that this tip is for those of you who are using cPanel (not everyone does). Once this option is enabled, your visitors should not be able to access your temporary links.
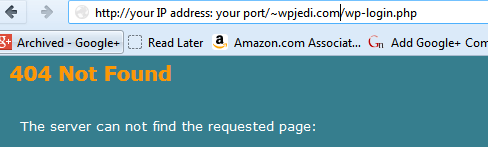
This won’t stop all hack attacks. But if you don’t want people to access your login page, you may want to disable temporary URLs and block access by all IPs but yours using NGINX.conf or .htaccess. It is always better to be safe than sorry.