Hack Prevention
31 Ways To Make WordPress Secure
Getting hacked is one of the worst experiences you can have as a webmaster. It is not possible to stop all hack attacks. But there are many things you can do as a webmaster to keep your server and site secure. Not taking the most basic security measures to protect your server could lead to disaster. In the past few months, we have covered plenty of tips and plugins WordPress webmasters can use to keep their websites secure. Here are 31 ways you can go about making your WordPress site harder to hack:
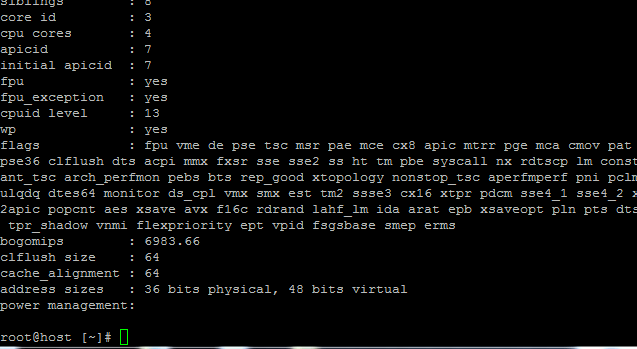
Know your environment: I can’t stress this enough. If you don’t know anything about Linux, Unix, Apache, and other solutions you are using to power your website, you are going to have a very difficult time keeping your server secure. For instance, those of you who know your Linux can rely on tools such as rkhunter to look for backdoors. The same approach applies to WordPress too. You should spend a considerable amount of time to get yourself familiar with how themes and plugins affect your site’s performance and security.
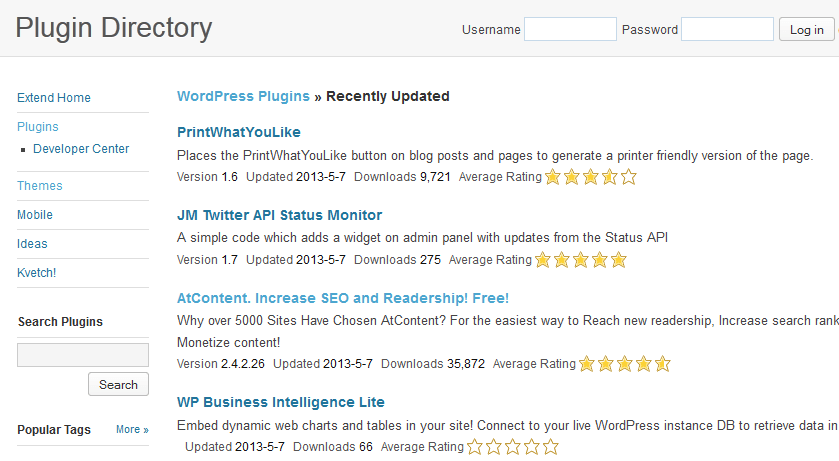
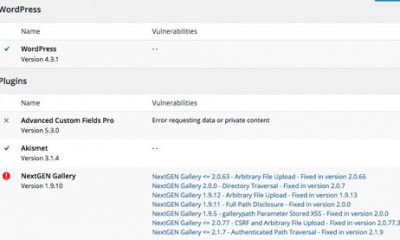
Keep WordPress themes and plugins updated: this should go without saying. We hear about vulnerabilities in certain themes and plugins each month. Many of them are updated by their developers regularly. If you don’t update old plugins or themes, you might get hacked. If you have multiple websites, you may want to rely on solutions such as ManageWP to handle the updates.
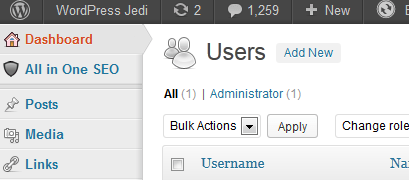
Remove Admin User: it is a very basic practice that many WordPress users follow these days. There are multiple ways to do it too (e.g. via phpMyAdmin).
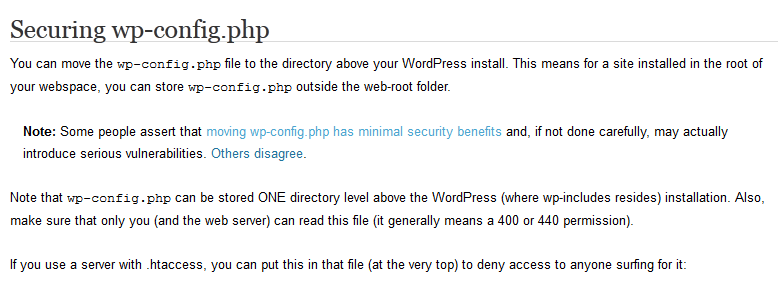
Move your wp-config file one level up: moving your wp-config.php file one directory up is a good practice (some argue it is not but I disagree). Make sure you get the permissions right.
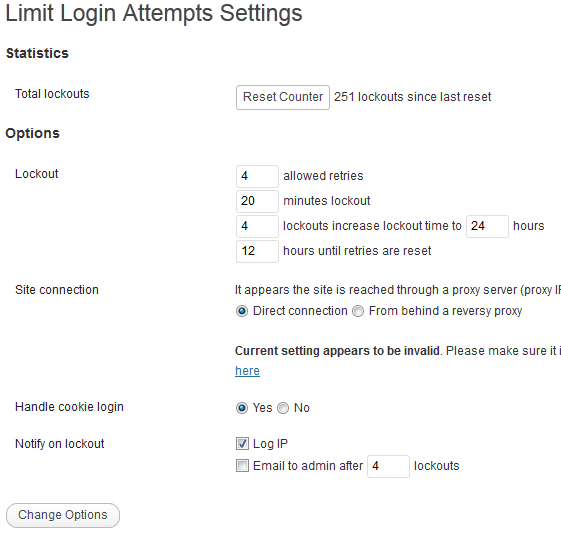
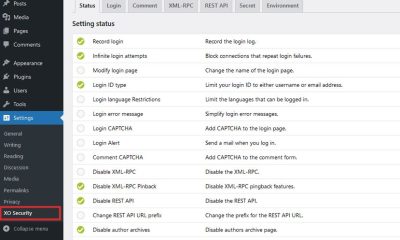
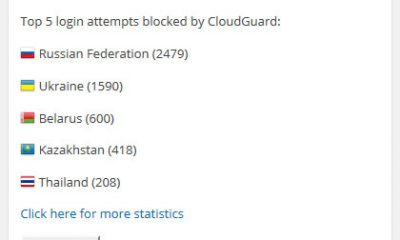
Limit login attempts: brute force attacks are not always sophisticated. But you should not let hackers mess with your login page. Using a plugin to limit login attempts is the least you can do to keep strangers out.

Enforce strong passwords: another simple step that many WordPress users miss. If your password is short enough that you can remember or guess it easily, then you are doing something wrong. You may want to rely on a plugin to make sure everyone on your website uses strong passwords.
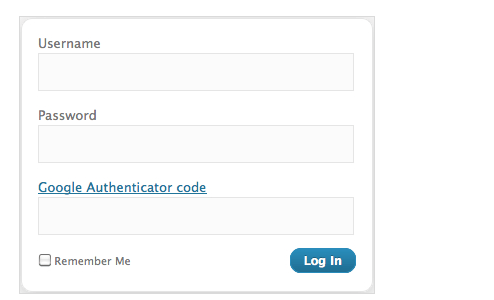
Add 2-factor authentication to your site: yet another way to make it harder for strangers to gain access to your admin pages. We have already covered plugins you can use to implement this.
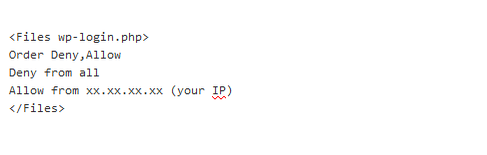
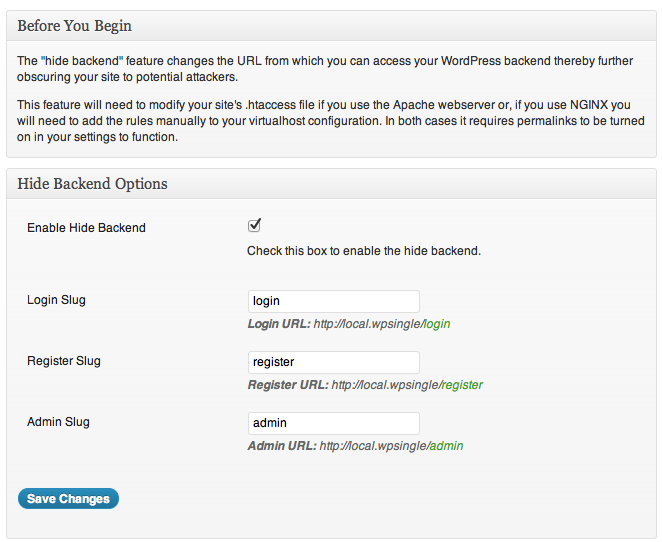
Restrict admin and login access by IP: you can do this by adding the appropriate restrictions to your .htaccess or nginx.conf file.
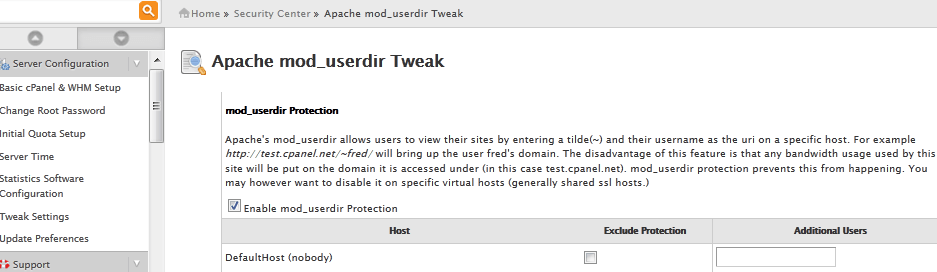
Disable temporary URLs: this might not work for everyone. But if you don’t need temporary URLs, there is no reason you should not disable them. We have already covered how these can be used to get around access restriction rules by IP.
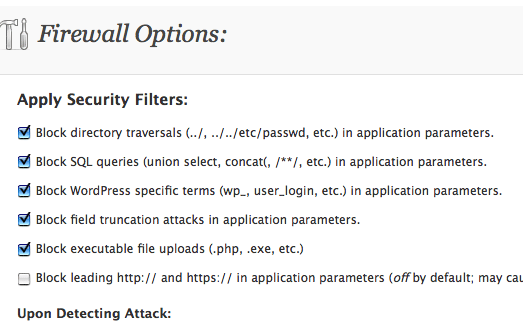
Add a firewall: not satisfied with the level of protection WordPress and server scripts offer? Adding a WordPress firewall may be the right idea for your site.
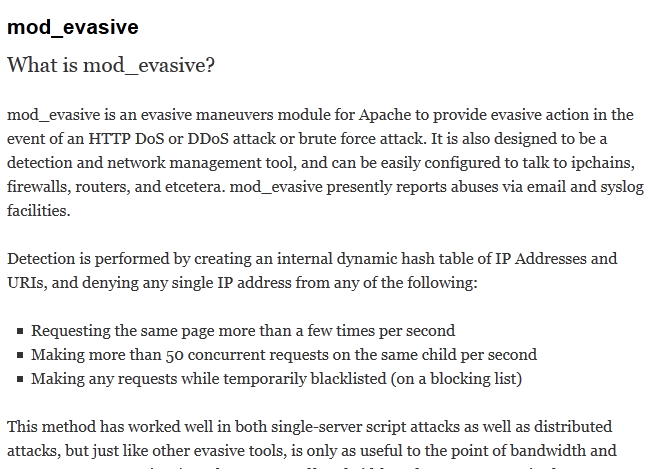
Fight back against DDoS: DDoS attacks can be very nasty sometimes. There are modules you can use to mitigate those types of threats. For instance, you can use mod_evasive to take evasive action when your site is being attacked.
Use third-party services to stop attacks: solutions such as CloudFlare are another layer of security you can pick up to stop spammers, SQL injection, and even DDoS attacks.

Watch out for CSRF: we don’t hear about CSRF attacks every day but you should make sure your site is protected against them. These plugins might help with that.
Scan your themes: there are plenty of fancy themes available for WordPress. That does not mean all of them are secure or safe to use. You should scan your theme files regularly to make sure there are no backdoors.
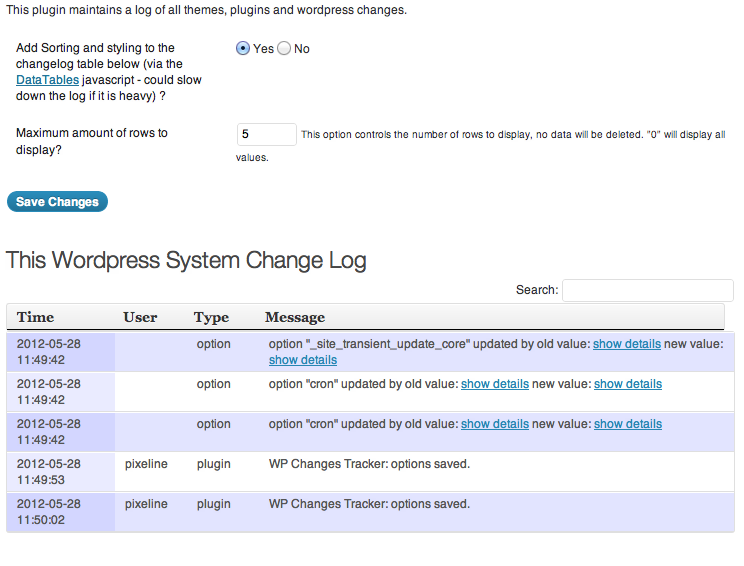
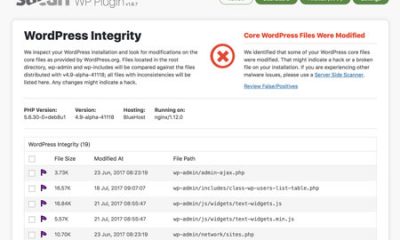
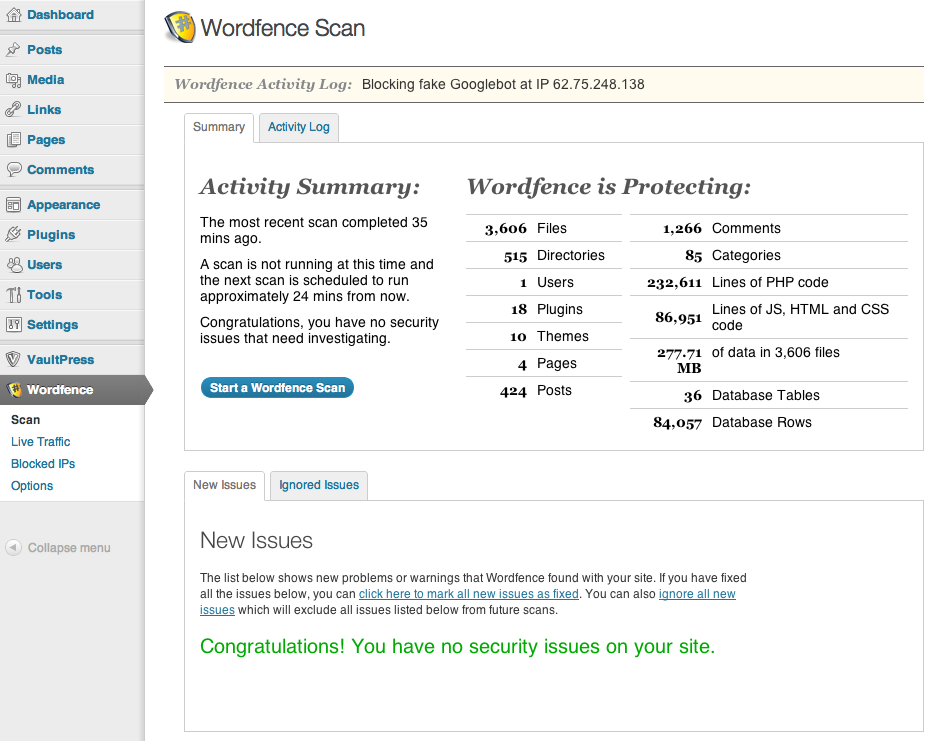
Monitor file changes: not all hack attacks happen overnight. Sometimes, hackers take weeks to implement their plan. By monitor file changes on your website, you will be able to catch them before they can do real damage.
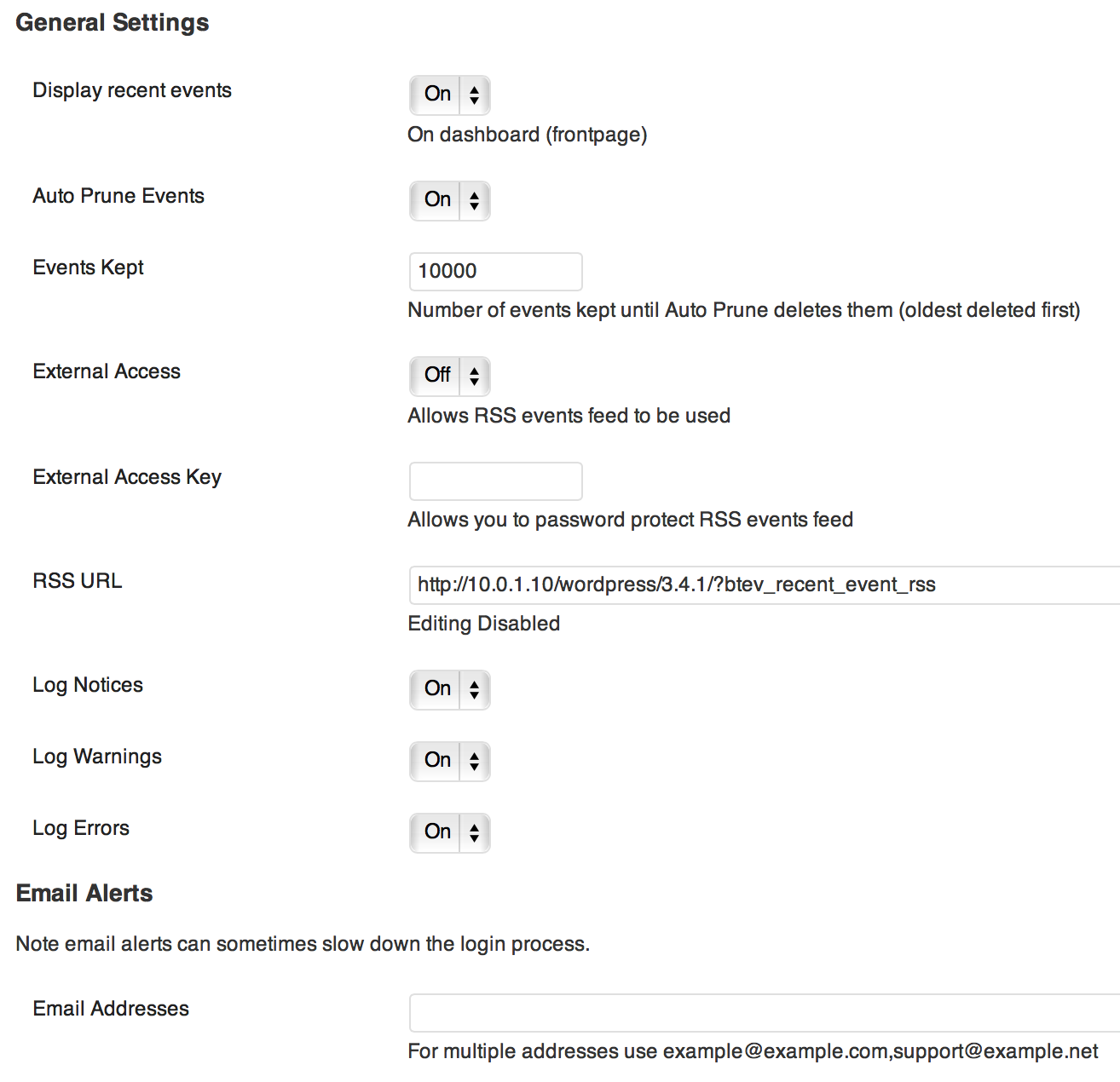
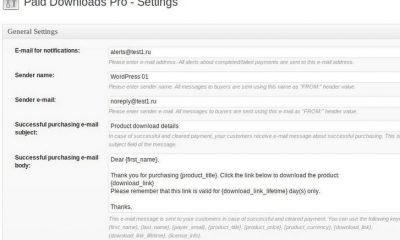
Monitor user activities: knowing what happens in your community and who may be trying to hack it is very important. You will always have a better chance to figure out what is going wrong when you can refer to activity logs.
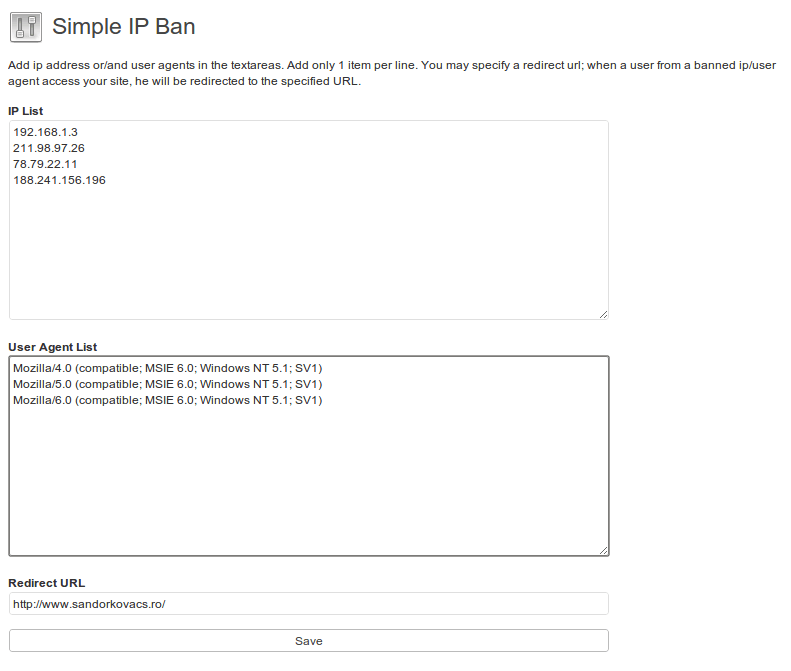
Ban suspicious users: not everyone who joins your community is there for a positive contribution. You should not hesitate to ban people who are trying to mess with your site. You can do so easily using plugins, .htaccess, or your Nginx conf file.
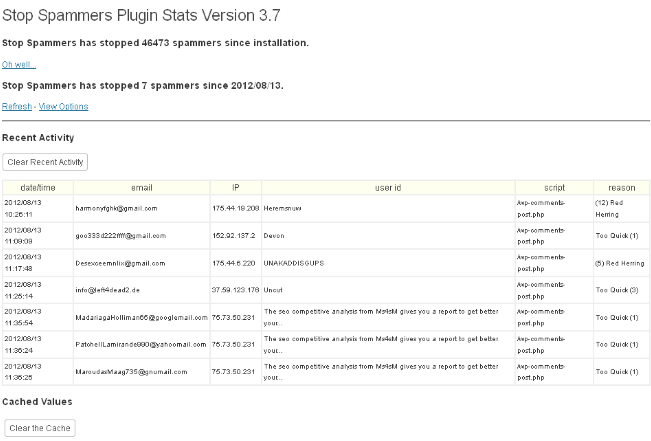
Remove spam registrations: this step is necessary if you allow registrations on your website. We have it disabled on all our sites for security reasons. But that may not be an option for everyone. You may want to use these plugins to remove or block spam registrations.
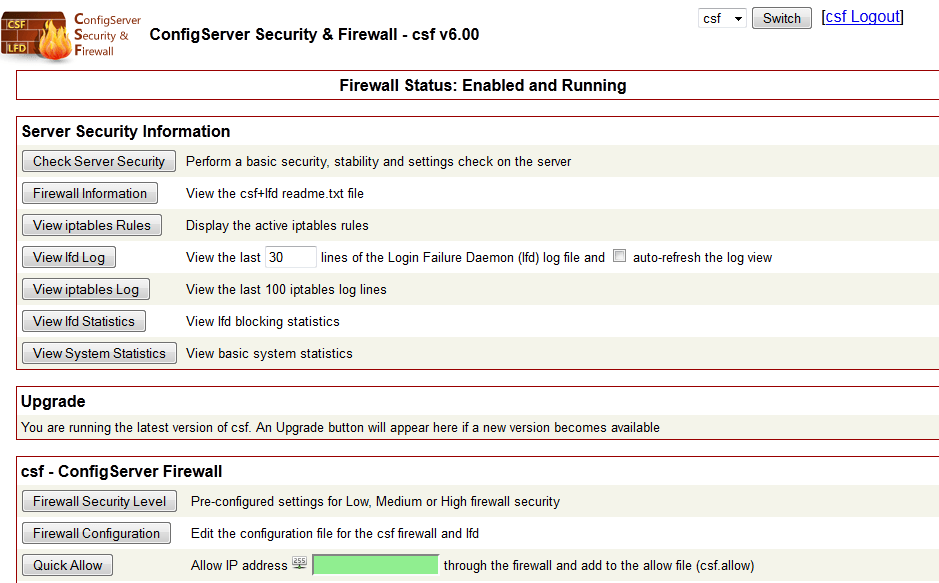
Optimize CSF: this won’t work for every WordPress site. But if you can install and manage CSF on your server, there is no reason not to do it. CSF can’t perform miracles but it does give you a better chance to keep your server protected from hackers.

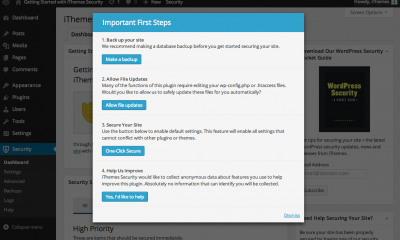
Backup your website: this is a no brainer. Disasters happen all the time. If you do not have your file backups stored offsite, you are going to have a difficult time bouncing back. VaultPress is a great backup solution for WordPress. These online backup tools can also get the job done well.
Use encryption when possible: backing up your website on a regular basis is a great idea. But where you put your files and how they are transmitted to an offsite location are important too. Encryption is your best friend here. Make sure you partner up with companies that have a solid track record when it comes to data security.
Use Secure FTP: you should not download/upload files to your server without enabling SFTP on your server first. Ask your web host to help you out if you don’t know how to do this.
User a safe computer: you should not use a computer that has viruses on it to log on to your website or server. Make sure you scan your computer regularly and only use safe computers to connect to your site.
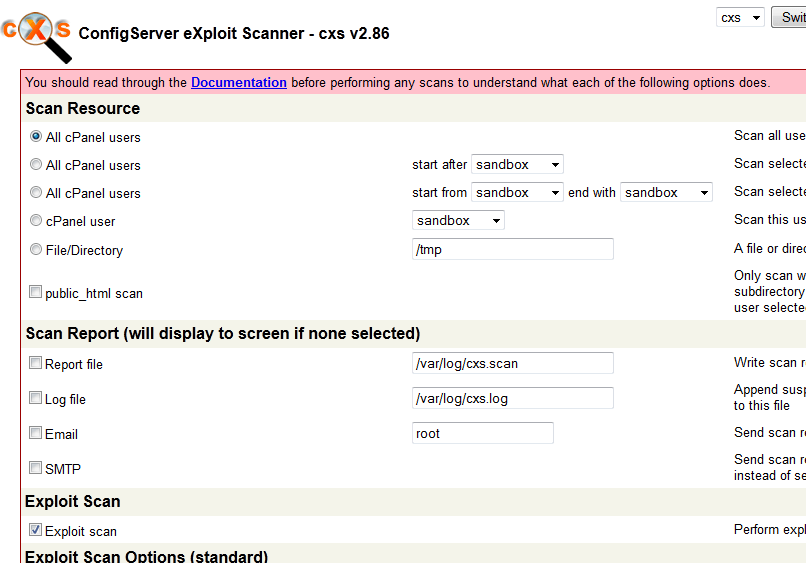
Monitor file uploads with CXS: ConfigServer eXploit Scanner is a premium add-on for your server that monitors file uploads and also looks for exploits on your server. It scan for viruses using ClamAV. Anti-Gumblar is worth checking out too.
.htaccess optimization: your .htaccess files are very important. You can use them to protect certain parts of your site and make your site run more smoothly. Don’t know how to use .htaccess to secure your site? There are plugins that can help you with the process.
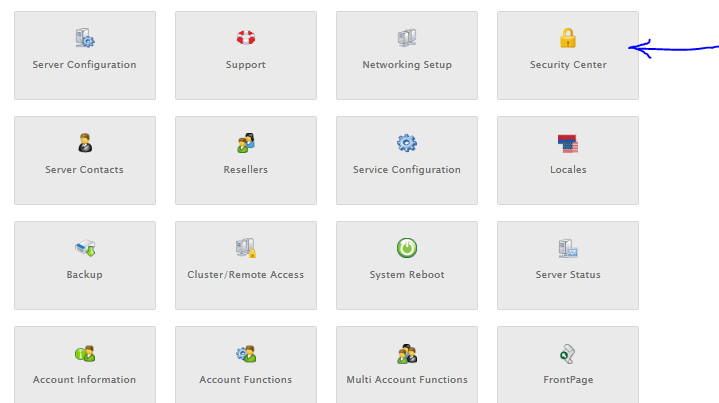
Protect cPanel access by IP: not everyone should have access to your server management software. If you are using solutions such as WHMCS, you can limit who can access them by whitelisting your own IP only.
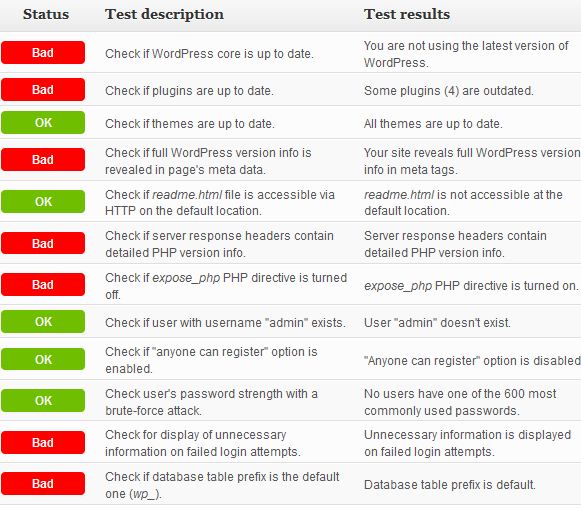
Follow basic & best practices: we have written many articles on other simple steps you can take to make WordPress secure. Even if you don’t have time to keep up with WordPress security articles, you can use these plugins to help you figure out the weaknesses of your site.
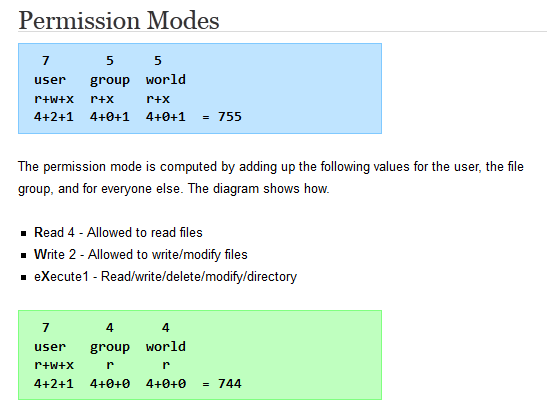
Set the right file permissions: WordPress.org has a lot of information on this. You should make sure your files have the right permissions.
Limit the number of plugins you use: we have been recommending this for a long time but a lot of folks in the WordPress community are not a fan of this approach. Not all plugin developers write secure code. Unless you rigorously test every plugin that you install on your website for security issues, you should try to limit your choices to those you feel confident about using.
Harden & optimize Apache or Nginx: this goes back to the very first point. Hardening Apache and Nginx takes work. You should take time to get yourself familiar with mod_security, mod_GeoIP, and other Apache modules that might help you keep your site secure. Understanding Nginx is important for webmasters planning to rely on it to run their server.
Do your research: Sucuri and other security blogs are worth keeping up with if you want to catch security hacks that may affect your sites in the future.
Keeping your website protected against all possible hack attacks is an ongoing process and can be difficult. It will be worth it in the long run. Getting hacked is much more painful anyway.